Multi-Factor Authentication (MFA)
Configure multi-factor authentication policies for the Wristband Identity Provider.
Multi-factor authentication (MFA) adds a second layer of verification on top of a user's primary login factor, requiring them to prove their identity using a separate method before gaining access. MFA is a feature of the Wristband Identity Provider. It does not apply to users authenticating through external identity providers, as those providers manage their own MFA enforcement. It consists of two distinct flows:
- MFA Enrollment: A user sets up their authenticator app for the first time
- MFA Challenge: An already-enrolled user is prompted to enter a verification code during login
For more context, see:
- Identity Providers → An overview of the Wristband IdP and the login methods it supports
- MFA Workflow → How the MFA enrollment and challenge flows work
MFA Policies
MFA is configured through policies under Security → MFA Policies in the Application View of the Wristband Dashboard. Policies set at the application level apply to all tenants by default.
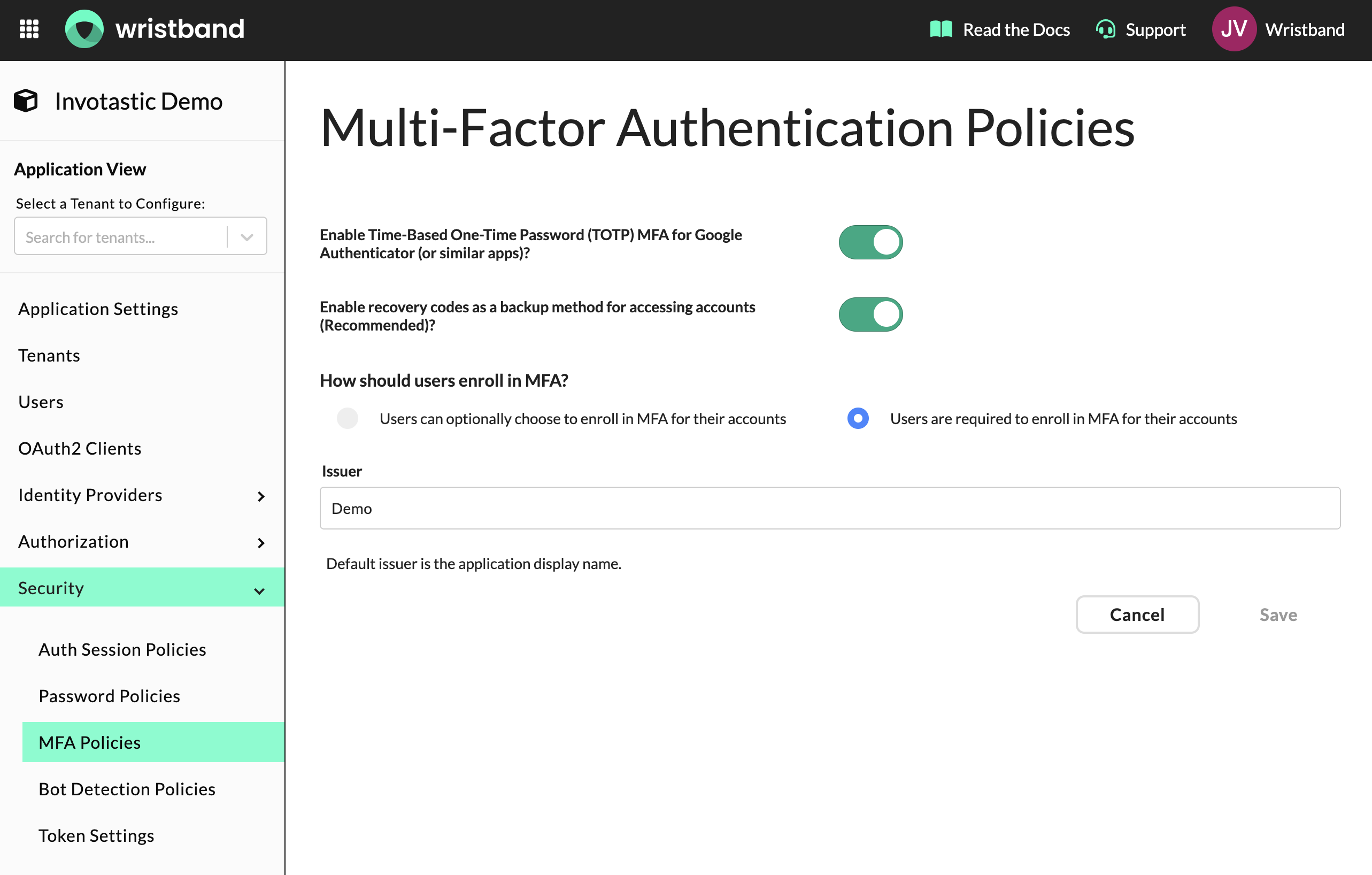
MFA Policies configuration in Application View.
The following settings are available:
- Enable TOTP MFA: Enables Time-Based One-Time Password (TOTP) authentication using an authenticator app such as Google Authenticator or Authy. TOTP must be enabled for MFA to be functional.
- Enable Recovery Codes: When enabled, users are issued a single-use recovery code after completing TOTP enrollment. This code allows them to log in if they lose access to their authenticator app. It is recommended to keep this enabled. Recovery codes are invalidated and regenerated each time a user re-enrolls.
- MFA Enrollment: Controls whether MFA enrollment is optional or required for users.
- Optional: MFA enrollment is not required. If you want users to be able to self-enroll, expose that ability in your own UI using the Enroll TOTP Auth Factor and Enroll Recovery Code Auth Factor APIs.
- Required: Users must complete MFA enrollment before they can access the application. Wristband will automatically prompt users to enroll during login, signup, user invitation, and password reset flows if they have not yet enrolled.
- Issuer: The name that appears in the user's authenticator app when they enroll. Defaults to the application's display name if left blank.
Tenant-Level Override
MFA policies can be overridden at the tenant level, allowing different tenants to have different MFA requirements. To configure a tenant-level override, select a tenant from the Select a Tenant to Configure dropdown in the Application View, navigate to Security → MFA Policies, and enable the tenant override toggle.
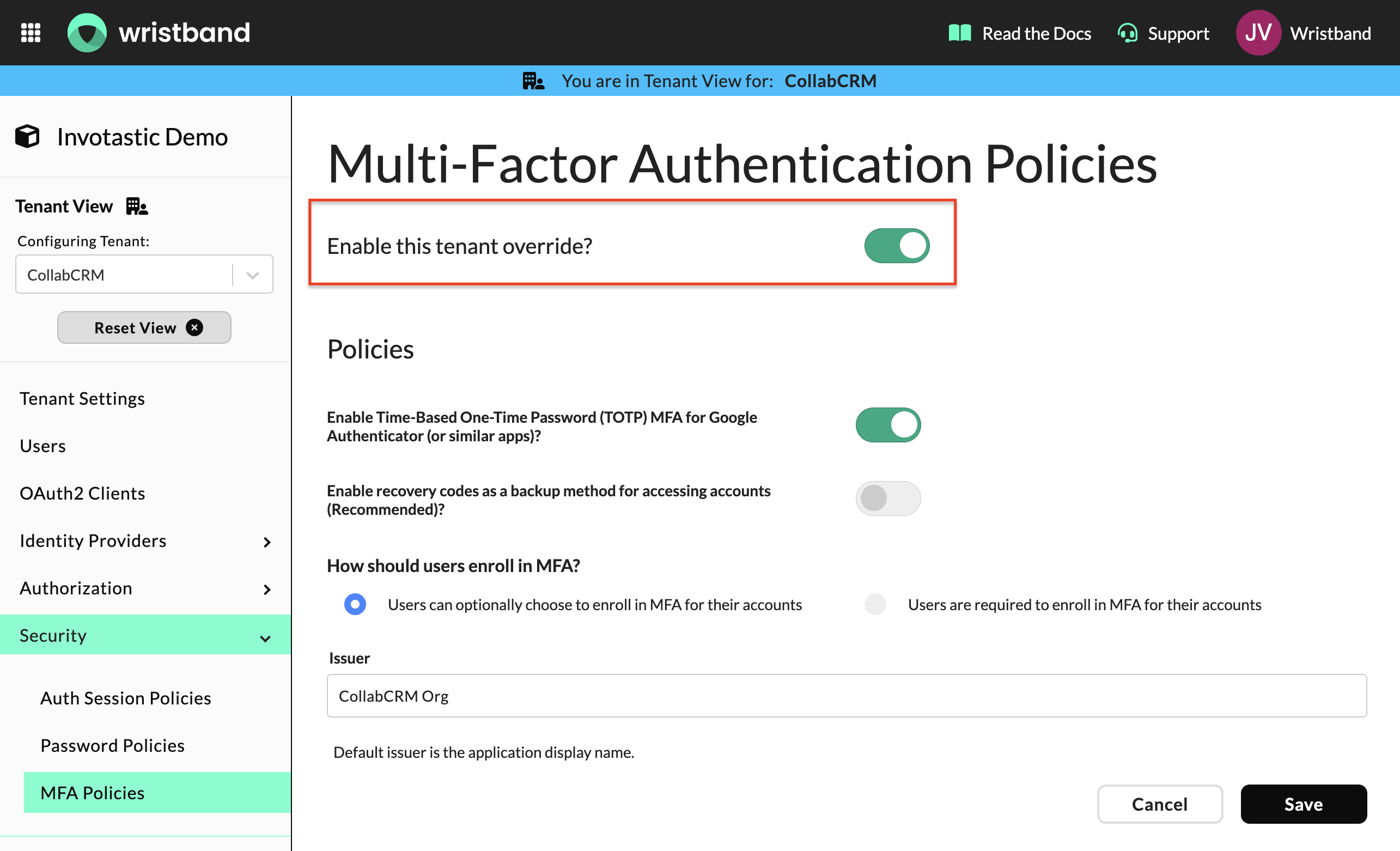
MFA Policies configuration in Tenant View with the tenant override toggle enabled.
Updated about 1 month ago